
10 Benefits of Cross-Platform Apps over Native Apps for Business
In the ever-evolving landscape of mobile applications, businesses are constantly presented with choices: cross-platform or native apps? Both
Read More
Outsourcing Software Development in 2024 and Beyond
Choosing a company to outsource your software development to has never been easy. And due to the current
Read More
10 Questions to Ask When Considering Custom App Development
With apps having become so popular, your business may wonder if it would be worth the investment to
Read More
Why You Might Not Need a Custom App
We might be able to save you some time. There's a chance that custom app development is not
Read More
Why Software Development Companies Require Discovery to Provide a Quote
So you've been contacting software development companies to get a quote for a custom software development project. Each
Read More
Resources for Mobile App Startups in Tampa
As a mobile app development company in Tampa Florida, startups in need of app development advice and services
Read More
How to Avoid Spelling & Grammar Mistakes in Your Software
Does your company have a process for avoiding spelling and grammar mistakes in your software? If not, or
Read More
How to Avoid Being Held Hostage by Your App Developer
Big Fish is an app development company in Florida. We sometimes receive calls from companies that are not
Read More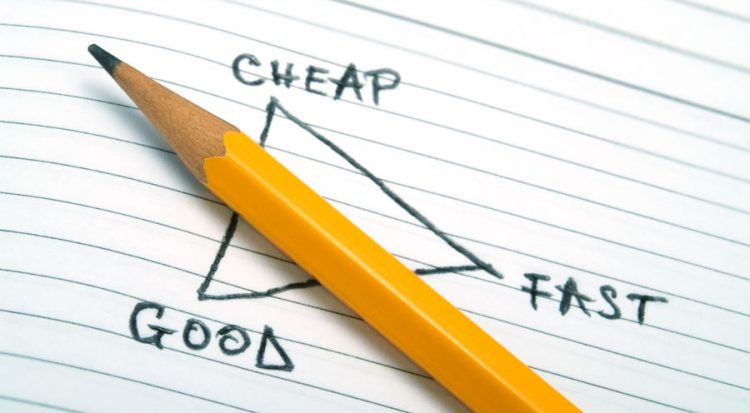
Fast, Cheap or Good? Pick Two.
So, you want custom software developed, and you need it fast, cheap and good? Sorry, you're out of
Read More
9 Reasons Why Your iOS App was Rejected by the App Store
Once your iOS app is complete, there's one last hurdle to get through. The app needs to be
Read More
How Long Does It Take to Develop An App
Big Fish is a boutique app development agency. With nearly ten years experience developing mobile applications, we can
Read More
What to Include In Your Mobile App Maintenance Plan
One of the biggest mistakes your company could make when planning a custom mobile app build, is not
Read More
iOS or Android: Which Platform Should We Develop Our App for First?
If you're here, your company is probably planning on developing a mobile app and deciding whether to start
Read More
Who Owns Your App’s Source Code?
Unless you've had a bad experience that put it on your radar, or you're a software developer, "source
Read More
Beyond Secure Software – How to Avoid a Data Breach
Your company has just had a beautiful new custom app developed. You’ve got salted and one way hashed
Read More
UX Teardown: The Duke Energy App
Before I dive into our UX Teardown of the Duke Energy app, a quick explanation of what a
Read More
Say “No” to Bad App Design
Say "No" to bad app design because -> How well your app is designed directly impacts how well
Read More
How We Use Mood Boards in UI & UX Design
Before diving into creating mockups, it's important to set the visual direction of an app or software design
Read More
What is an App Prototype & How You Can Benefit from Making Your Own
You may know intrinsically that the right mobile app will make your workers more productive, your customers happier,
Read More
Our Thoughts on Flutter for Cross-Platform App Development
If you're having an app developed, you'll need to decide between native app development and cross-platform app development
Read More
Hiring an Agency vs Hiring Freelance Mobile App Developers
If you've been tasked with putting together a team to develop your company's mobile app, you have a
Read More

